The Audit Automation Revolution (Or: How I Learned to Sleep Again)
Ever tried explaining to non-technical executives why their “industry-leading security posture” actually resembles a scarecrow with missing limbs? That was me a month ago, watching faces fall as I revealed their documentation had more holes than my attempts at knitting (current hole-to-scarf ratio: approximately 3:1).
Unfortunately, in this article, I won’t be sharing code samples of what I’ve done. Instead, I’ll refer to some of the data models I’ve been using, and you can figure it out yourself or connect with me on LinkedIn. If you’re interested, I’d be happy to share more information. Read on or … whatever! ;)
The Real Problem
The problem wasn’t their security - it was their approach to security documentation in general. Instead of just fulfilling an external requirement, they made themselves vulnerable. For every security requirement coming from outside, they were actually creating five more internally which they never turned out to fulfill with their technical controls.
Meanwhile, this has been a crazy weekend expanding on what I’d been developing secretly for last few months what I dramatically call “The Trilogy of Not Losing Your Mind During Audits”: context embedding, Stage 1 verification, and Stage 2 validation.
Context Embedding: The Digital Sherlock Holmes Phase
Traditional audit preparation looks like me trying to assemble flatpack furniture after losing the instructions - chaotic, frustrating, and likely to end in tears.
Context embedding with AI transforms this experience entirely.
Here’s how it works in real life:
Requirement Relationship Mapping: AI analyzes frameworks to identify connections between requirements faster than my border collie spots tennis balls in tall grass. Requirements that seem different often overlap like my neighbor’s tree branches in my garden - technically separate but practically inseparable.
Documentation Relationship Analysis: Instead of manually reading through policy documents (an activity I rank just above getting a root canal), AI creates a semantic map showing how documents reference each other. During one audit, we discovered a client’s incident response procedure referenced a non-existent escalation matrix, which referenced an outdated contact list, which referenced… you get the idea. It was the security documentation equivalent of those infinite mirror reflections.
Internal Requirement Extraction: The hidden gem! AI identifies statements like “The organization shall review access quarterly” buried in policies. These self-imposed requirements are the organizational equivalent of drunk online shopping - commitments made enthusiastically that nobody remembers the next morning.
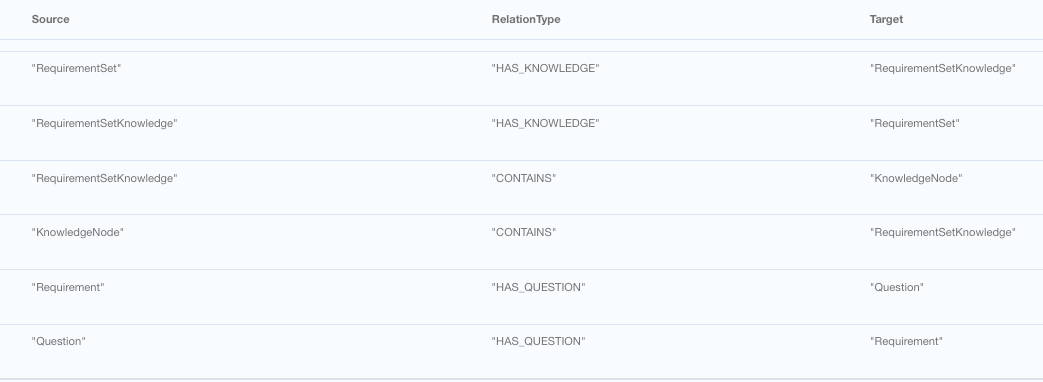
However, there is a big but in this part. The but part is that doing this manually by using AI tools or just using a standard n8n worklow type of automation will not really work. What you would need to do, you would need to create graph database with quite complex relationship models.
I once extracted 53 internal requirements from a client’s documentation. Their CISO made the same face my cat does when I accidentally step on her tail - shock, betrayal, and the dawning realization that somebody’s going to pay for this because it turns out “once you say you do it, you actually have to do it”.
Stage 1: The Great Documentation Alignment
Stage 1 uses AI to answer the eternal question: “Do we actually have policies and procedures that match our claims, or are we just making things up like my excuses for not going to the gym?”
The AI automation process:
Classification: Determines if requirements need documentation verification - because some things actually don’t. I once spent three hours looking for a client’s “data destruction procedure” before realizing they were a cloud-only company that never handled physical media. That’s three hours of my life I’ll never get back, much like the time I spent learning to play the recorder in primary school.
Document Search & Match: AI searches repositories to identify relevant documents faster than I can find my car keys (which, admittedly, is a low bar). One client swore they had “robust encryption standards” until our AI found their so-called standards consisted of a single sentence: “Use encryption when necessary.” Helpful as a chocolate teapot, that one.
Gap Analysis: Identifies missing documentation with brutal efficiency. The AI doesn’t sugarcoat findings like humans do. It won’t say “opportunity for improvement” - it just flatly states “completely missing,” much like my filter when I’m on my third coffee of the day.
I witnessed a security director visibly age during a presentation of Stage 1 results. “But we passed our last audit!” he protested. Yes, and I once convinced my niece I could make coins appear from behind her ear - some illusions are easy to maintain until someone looks closer.
DISCLOSURE: Remember, in the beginning of this paragraph, I said “fast”. The honest answer: “normal document package takes around 4 hours or so to do full analysis of it.”
Stage 2: Show Me The Evidence (Or: Prove It!)
If Stage 1 is about finding what you claim to do, Stage 2 is proving you actually do it - the difference between my New Year’s resolution to learn Spanish and the reality that I still can’t order anything beyond “cerveza, por favor.”
AI transforms this stage from a scavenger hunt into a precision operation:
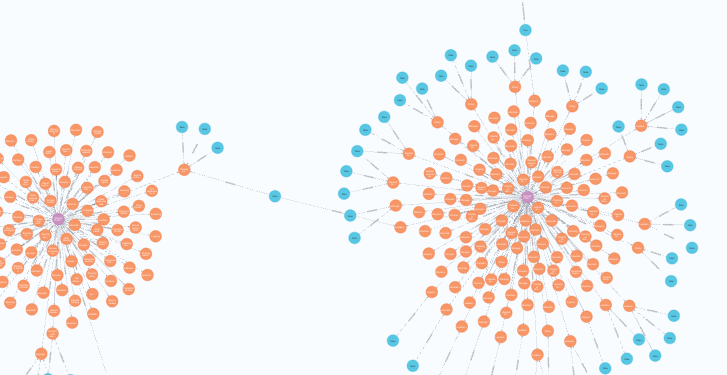
Limited representation of just a few questions to verify specific short set of requirements in Neo4J
Custom Evidence Questions: AI generates tailored validation questions based on documentation found in Stage 1 and those sneaky internal requirements. Instead of generic “Do you review access?” questions, it asks “Please provide the last three quarterly access reviews from March, June, and September as specified in Policy SEC-035, section 4.2.” Try wriggling out of that one!
Evidence Validation: AI pre-analyzes submitted evidence to check if it actually satisfies requirements or is just adjacent to them - like my attempt to count gardening as exercise. (It’s not, apparently, no matter how many times I argue about digging being a core workout.)
Continuous Compliance Tracking: Identifies ongoing obligations and creates schedules to verify them throughout the year, not just during panic-driven audit season. This is the difference between my daily flossing (theoretical) and my week-before-dentist-appointment flossing marathon (actual).
During one audit, our AI identified that a client had committed to monthly security testing in their customer-facing documentation. Their actual testing schedule? “Whenever Gary remembers,” which turned out to be roughly once every leap year. The gap between claimed and actual practices was wide enough to park a cruise ship sideways.
The Life-Changing Magic of Automated Audits
Automated audits using AI aren’t just faster - they’re fundamentally different. Like comparing my attempt at cutting my own hair during lockdown to an actual professional haircut. Same general concept, wildly different results.
Internally it means for internal audit preparation time now I can reduce from six weeks to three days for a 100+ people organization. In another case we had customer discovering their actual security posture was stronger than their documentation suggested - they were doing the right things but not writing them down, like my grandmother’s cooking recipes that existed entirely in her head. And don’t mention the verbal storm I had to sit through then listening how “stupid all the EU regulations are and why we don’t need them” while actually they were doing MORE…
The most satisfying moment? Watching a use case for the system to identify 27 areas where a customer could simplify policies without reducing security effectiveness. Their documentation diet was so successful that their security handbook went from “War and Peace” dimensions to something people might actually read without developing carpal tunnel syndrome.
Embrace The Future (It’s Less Painful Than You Think)
If you’re still doing manual audits, you’re the security equivalent of someone still using a Nokia 3310 in the age of smartphones. It works, technically, but you’re missing out on a whole new world of capabilities and a lot more free time.
Next-generation audits with AI context embedding and two-stage verification don’t just make audits bearable - they make them valuable. And they’ll save you from the embarrassment of claiming complete compliance only to discover you have the security documentation equivalent of swiss cheese.
And isn’t avoiding embarrassment what security is really all about? Well, that and protecting critical assets. But mostly avoiding embarrassment in front of executives. Trust me, I speak from experience.
P.S. If your security documentation is perfect and requires no improvements, congratulations! You’re either lying to yourself or you’re from an alternate dimension where documentation writes itself. Either way, I’d like to hear your secrets.
